Mobile apps are everywhere. Whether it’s a banking app, a fitness tracker, or a marketplace for local goods, almost every business building digital products today has a mobile application at its core. But while app development has accelerated, security often struggles to keep up.
Mobile application testing is a critical part of a secure software development lifecycle. Unfortunately, many development teams still underestimate the risks, or assume that app stores, operating systems, or third-party libraries will take care of it all. They don’t.
There are two sides to mobile application security testing: the application itself, and the API it talks to. Both need proper penetration testing.
Testing the App Itself
Most mobile apps run on iOS or Android, and a lot of teams rely heavily on the security of those platforms to protect the app itself. While Apple and Google do a good job, relying on device-level security alone is risky. Once someone has physical access to the phone, or has jailbroken or rooted it, your app’s internal security is the only thing standing between them and your users’ data.
Good mobile app penetration testing looks at:
-
Poor data hygiene — is sensitive data cached, logged, or stored insecurely?
-
Insecure local storage — are hardcoded secrets or credentials accessible from the app binary?
-
Weak protections — does the app allow users to bypass authentication or escalate privileges?
-
Reverse engineering — can someone decompile the app and understand how it works?
-
Insecure code — are you using vulnerable libraries or outdated SDKs?
The OWASP Mobile Top 10 is a solid reference point here. It covers key mobile app security risks like insecure authentication, improper platform usage, and insufficient cryptography. If your app hasn’t been tested against these, it’s vulnerable — plain and simple.
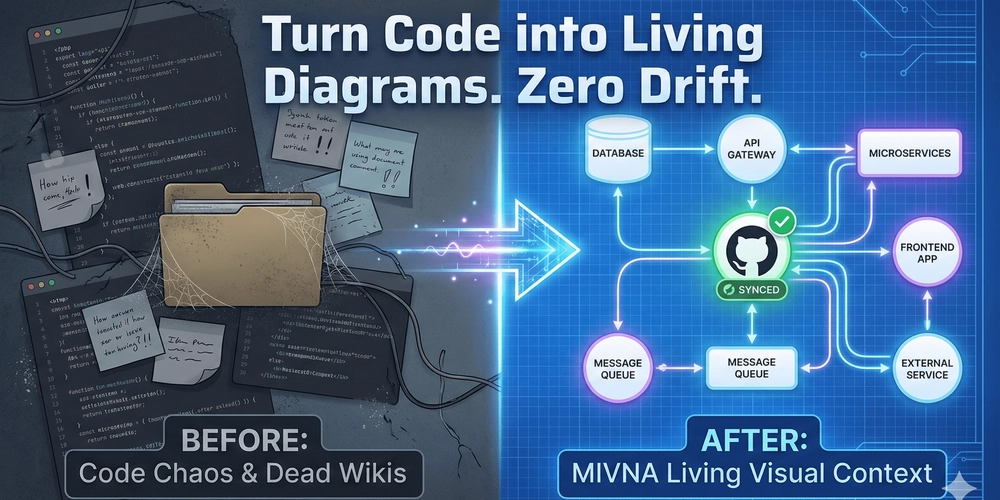
Testing the API Behind the App
The second half of the equation is your app’s backend, the API it talks to.
Too many mobile apps act like the API is some black box, assuming that only the app can talk to it. But the truth is, anyone can send requests to your API with the right tools, Postman, Burp Suite, or even curl. If your API doesn’t validate requests properly, or if it exposes too much data, it becomes a target.
API penetration testing helps identify:
-
Broken object-level authorisation – can one user access another’s data?
-
Excessive data exposure – are you unintentionally releasing sensitive data?
-
Lack of rate limiting – can this be abused to adversely affect your service?
-
Poor authentication – can it be easily bypassed?
-
Injection flaws – does the API prevent injection attacks such as SQLi?
All of these are covered in the OWASP API Security Top 10, which should be considered essential reading for any team developing a mobile or web application.
Real-World Risk: What Happens if You Don’t Test?
Let’s say someone gets hold of a user’s device. Maybe it’s lost, stolen, or handed in for repairs. If your app stores sensitive data locally, like session tokens or personal info, that’s an issue. Or worse, if you’ve hardcoded credentials to your API inside the app (and yes, this still happens), then you’ve just given an attacker everything they need to target your backend systems.
We’ve seen real-world examples where apps left sensitive endpoints unprotected or trusted the app too much and didn’t verify requests on the server side. In one case, an app allowed anyone to pull down full user profiles just by changing a user ID in the request. That’s the kind of thing that proper penetration testing picks up before it becomes a news headline.
What Mobile Application Penetration Testing Involves
At Cyberoptic Security, we break mobile application testing into two focused phases:
-
Mobile app testing — reviewing how the app handles data, how it’s built, and how resilient it is to reverse engineering and tampering. We simulate what an attacker could do with a compromised device or a modified app binary.
-
API testing — analysing the API endpoints your app communicates with. We test access controls, input validation, authentication mechanisms, and other key areas where APIs often fail.
This combined approach provides a clear picture of how your app would stand up to real-world attacks.
Why Dev Teams Should Care
Mobile app development is fast-paced. MVPs get released quickly. Security can get pushed aside for speed. But in 2025, security is no longer a nice-to-have, it’s an expectation. Users trust your app with their data, and regulators increasingly expect responsible handling of personal information.
Pentesting your mobile application (and its API) helps protect your users, your reputation, and your business. It’s far more cost-effective to find these issues early than to clean up after a breach or privacy complaint.
Useful Resources for Mobile and API Security
These are excellent resources for developers and security teams. In addition to good development practices, mobile app penetration testing is also highly recommended.
Need Help?
At Cyberoptic Security, we work with companies to deliver practical, hands-on mobile app and API security testing. We take the time to understand your tech stack, your threat model, and your release cycle. Whether you’re launching your first app or scaling to thousands of users, we’ll help you do it securely.
If your development team is building or maintaining a mobile app, now is the time to invest in security testing. Don’t wait for something to go wrong.