Use-case: When publishing tech docs or pushing script files to Halo’s content library, your requests may get blocked by your Web Application Firewall.
Fix: Add a narrowly scoped allowlist (whitelist) in SafeLine WAF for Halo’s API endpoints—carefully.
Heads-up: This is a convenience rule. It trades some protection for functionality. Validate in staging, audit frequently, and keep the scope as tight as possible.
Why this happens
Halo’s editor and resource library push content via PUT/POST to:
apis/content.halo.runapis/api.console.halo.run
Script-like payloads (e.g., .sh, .ps1, inline code blocks) and certain headers can trigger WAF inspections and get blocked.
Why SafeLine WAF
SafeLine WAF (by Chaitin) focuses on intent detection and gives you granular Web ACLs to handle edge cases like this without turning off protection globally. It’s popular across homelab and production setups and easy to operate.
What we’ll allow
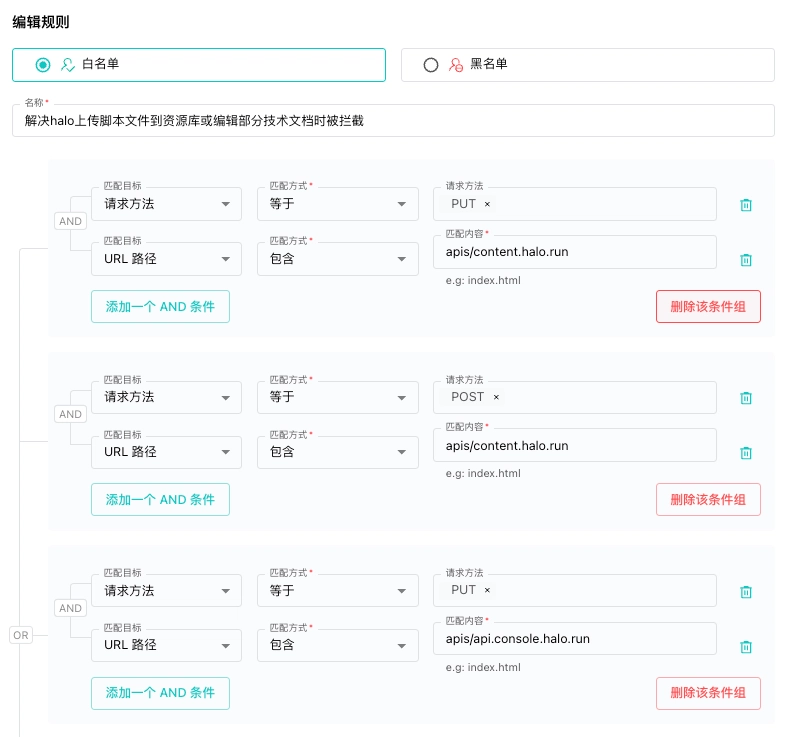
We’ll create one allowlist rule group (no blacklist entries) that only permits:
- Methods:
PUT,POST - Hostnames:
apis/content.halo.run,apis/api.console.halo.run - Your trusted source IPs (optional but recommended)
- Your Halo admin paths only (optional)
Supported SafeLine version: 7.3.0 and later.
How to configure in SafeLine
UI path may vary slightly by release. The logic below maps 1:1 to SafeLine’s Web ACL builder.
-
Create a new rule group
- Name:
Allow Halo Uploads (Scoped) - Description:
Allow PUT/POST to Halo APIs to fix editor/library blocks - Default action: Follow global policy
- Name:
-
Add a rule (Allow)
-
Match ALL of the following (AND):
-
HTTP Method is
PUTORPOST - Request Host equals one of:
apis/content.halo.runapis/api.console.halo.run-
(Optional, strongly recommended) Source IP/CIDR in your admin/VPN ranges
e.g.10.0.0.0/24, 192.168.1.0/24 -
(Optional) URL Path starts with your admin routes
e.g./api/,/content/
-
HTTP Method is
-
Action:
Allow (bypass further checks) - Order: Place above generic bot/automation blocks
- Expires: Add a time-to-live if your SafeLine version supports it (e.g., 7 days)
-
Match ALL of the following (AND):
-
Attach the rule group
- Scope to the site/app that fronts your Halo instance (don’t attach globally).
-
Audit & monitor
- Enable request logging for this rule
- Add alerts on unusually large uploads or spikes in request volume
Rollback plan
If something looks off:
- Disable the rule group (don’t delete—keep it for diff and audit).
- Re-enable standard inspection/bot rules.
- Check recent logs filtered by host =
*.halo.runto understand what slipped through. - Re-introduce the rule with tighter scope (IPs, paths, size limits).
Security tips (Keep the blast radius small)
- IP-scope: Limit to your VPN/admin CIDRs whenever possible.
- Path-scope: Only allow routes Halo genuinely uses to upload/edit.
-
Rate limiting: Add a per-IP limit (e.g.,
100 req/min) on the same host/path. - Body size guard: Cap max upload size to what Halo needs.
- Short-lived allow: Use expiring rules for exceptions.
- Logs on: Keep verbose logs for these endpoints, rotate, and review weekly.
TL;DR
Halo uploads getting blocked? In SafeLine WAF, add a scoped allow for PUT/POST to apis/content.halo.run and apis/api.console.halo.run, ideally restricted by source IP and path. Log everything, rate-limit aggressively, and expire the rule when you no longer need it.
Join the SafeLine Community
If you continue to experience issues, feel free to contact SafeLine support for further assistance.