Introduction
As part of my continuous exploration of application security, I worked on a practical project to comprehend the practical dangers of sending data without encryption. Even though theoretical knowledge is important, nothing helps to cement comprehension like extracting real-time credentials from network data. With the “HTTP Credential Sniffer & Secure Transmission Analyzer,” I delved deeply into the principles of threat modeling, compliance impact analysis, and cleartext protocol exploitation.
The precise steps I took to locate, take advantage of, and record a serious vulnerability on the test site testphp.vulnweb.com will be outlined in this technical walkthrough. We’ll demonstrate the vulnerability using popular pentesting tools like Wireshark and tcpdump, and then we’ll contextualize its implications beyond a CVSS score.
https://github.com/Samuelade24/HTTP-Credential-Sniffer—Secure-Transmission-Analyzer
Project Scope & Reconnaissance
Finding a target that was sending login credentials via HTTP and capturing them to illustrate the risk was the obvious goal.
Step 1: **
**Target Identification and Service Discovery
First, I looked for hosts that had HTTP port 80 open. I used the purposefully vulnerable Acunetix testphp.vulnweb.com for this project.
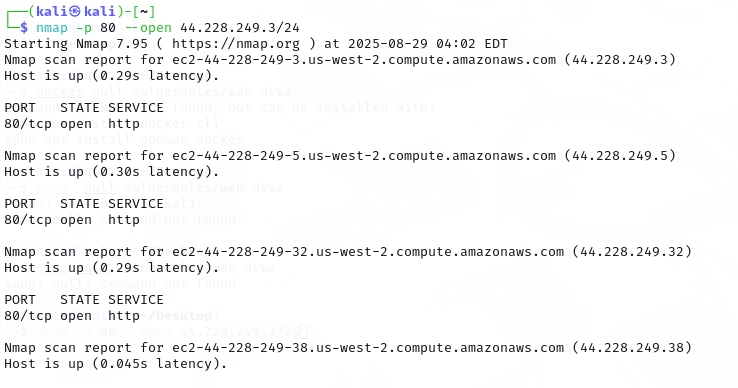
Using this Command: nmap -p 80 –open 44.228.249.3/24
Live hosts with port 80 open within the specified range are found by this scan.
Principal Finding: Port 80 received a response from the target server. It was then verified that it did not reroute to HTTPS (TLS), which would have encrypted the communication.
The next Command i used was: curl -I http://testphp.vulnweb.com/login.php
This verified that the site was using HTTP exclusively to serve the login page, which was the first significant setup error.
Important Recommendation:
Improving Defenses & Addressing Cleartext Credential Transmission
This practical security analysis project which successfully intercepted user credentials sent in plaintext via HTTP served as the basis for this advise. The results highlight a serious technological, financial, and compliance issue that is widespread yet critical.
These are the short- and long-term steps that organizations needs to follow, if ti were to be in a real life scenerios.
Immediate Best Practices & Remediation (Next 24-72 Hours)
These are quick-win, non-negotiable measures that deal with the most serious weakness.
Enforce HTTPS Everywhere: Getting rid of HTTP completely for all services that interact with users is the top priority.
Action to be Taken: Put HTTP to HTTPS redirects into place. Set up your web servers, such as Apache and Nginx, to automatically reroute all HTTP traffic to HTTPS. Nginx Configuration Example:
server {
listen 80;
server_name yourdomain.com;
# Enforce HTTPS redirect for all requests
return 301 https://$server_name$request_uri;
}
Deploy HSTS (HTTP Strict Transport Security). This instructs browsers to only connect via HTTPS for a specified period, preventing SSL-stripping attacks and user override.
Add to your HTTPS server block:
add_header Strict-Transport-Security “max-age=31536000; includeSubDomains” always;
Use Free, Automated Certificates. Cost is no longer a barrier. Use Let’s Encrypt and the certbot tool to automatically obtain and renew TLS certificates.
Command: sudo certbot –nginx -d yourdomain.com –redirect
Disable Current Sessions
Force the termination of all running user sessions after implementing HTTPS. This guarantees that session tokens, often known as cookies, sent over HTTP are rendered invalid and need to be reestablished via a secure channel.
Short-Term Strategic Enhancements (Next 2-4 Weeks)
Move beyond the basics to build a more resilient security posture.
Use Secure Credential Management Procedures
The best practice is to never send credentials using URL parameters or GET requests. These are recorded in online analytics tools, server logs, and browser histories. Use HTTPS just for POST requests.
Using and enforcing CSRF tokens on all authentication and state-changing forms is best practice. This stops hackers from deceiving logged-in users into sending harmful requests against their will.
The best course of action is to transition to modern authentication. Take into account putting in place protocols like OpenID Connect or OAuth 2.0, which are made to securely manage credentials.
Enhance Network Security Controls
Segmenting your network is a best practice. Databases and other critical servers shouldn’t be directly reachable from the web-facing section. Even in the event that a front-end server is compromised, this restricts the attacker’s lateral mobility.
The best course of action is to prevent Layer 2 attacks. Protect yourself from the ARP spoofing methods used in the project.
For network engineers: Turn on Dynamic ARP Inspection (DAI) and DHCP Snooping on your network switches. These characteristics stop fraudulent ARP packets from contaminating the ARP tables on the network.
Implement a Web Application Firewall (WAF)
Install a WAF before your application. A WAF can assist in thwarting a variety of assaults, such as:
- Assaults that employ compromised username/password lists to stuff credentials.
- Attempts at Cross-Site Scripting (XSS) and SQL Injection.
- Unusual patterns of requests that could point to automated scanning.
Long-Term Cultural & Procedural Changes (Ongoing)
True security is a process, not a product. Learn to incorporate security into the SDLC (DevSecOps): Security cannot be neglected. Move to the left.
Take action:
- To identify code vulnerabilities before they are released, incorporate SAST (Static Application Security Testing) tools into your CI/CD workflow.
- To Check for vulnerabilities similar to the one found in this project by using DAST (Dynamic Application Security Testing) tools to examine active applications, such as staging environments.
- Require developers to complete security training. Instruct students on secure coding techniques and typical vulnerabilities (OWASP Top 10).
Proactive Monitoring and Response
- Install a SIEM (Security Information and Event Management) system for proactive monitoring and response.
- Gather logs from your network devices, web servers, and authentication systems.
- Set up notifications for unsuccessful login attempts, successful logins from odd regions, and any attempts to reach HTTP endpoints.
- Take action by creating an official incident response plan. Article 33 of the GDPR, which mandates breach notification within 72 hours, was violated by the project. If an actual incident happens, your team needs to know exactly what to do.
Commit to Continuous Assessment
- Make a commitment to ongoing assessment by planning frequent vulnerability assessments and penetration tests.
- Perform internal scans every three months.
- At least once a year, hire certified ethical hackers from outside your company to test your infrastructure that faces the outside world. What old eyes miss is seen by new ones.
Key Learnings for Stakeholders
A number of important lessons are reinforced by my project:
- “Test/Internal” isn’t a valid substitute. Test settings can contain actual or sample data and frequently resemble production settings. Since they are a frequent point of entry for attackers, they also need to be protected to the same degree.
- Not a ceiling, but a floor, is compliance. A minimal need is to comply with PCI-DSS, GDPR, or ISO 27001 standards. Exploitable weaknesses are what adversaries are interested in, not your compliance checklist. Develop security that goes beyond frameworks, but use them as a guide.
- The Technical teams and management can’t deny the vulnerability because it can provide a timestamped packet capture (cleartext.pcapng). It turns a theoretical risk into a real danger to business.
- The threat is low-cost and real. It has been shown that the tools needed to carry out this assault (Ettercap, Wireshark) are free, and the methods are well-established. Your defense needs to be proactive.
In conclusion
Cleartext credential interception is a serious and completely avoidable issue. You may safeguard user data, your business’s reputation, and your bottom line from serious financial and regulatory harm by putting the layered strategy described above into practice, which includes both short-term technical solutions and long-term cultural changes.





teddpegiljpoejhtwxyhujzszzsslx